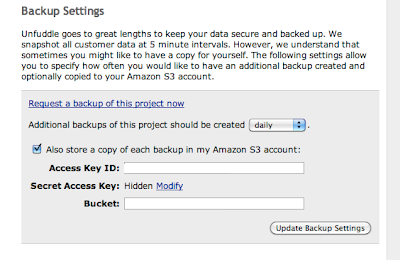
Unfuddle asks for the 'access key id' and 'secret access key' in order that their scripts can write direct to your bucket. This is great, but armed with both those keys an attacker can easily access ALL of the buckets associated with that account. Our main account has potentially sensitive data in some of the buckets, so there is obviously no way we'd share the keys to that account with anyone.
Instead, what we can do is to create a completely new AWS account, and from the main account grant access to the new account ONLY to the bucket that'll contain the unfuddle backups. Note that you do not need a credit card number to do this, as the new account will not 'own' any of its own buckets. Also note that usage charges for the backup bucket will be applied to the main account.
Here's how: (note this tutorial requires Cyberduck, a free S3 and FTP client).
- Make a new email address such as aws-myproject@example.com.
- Go to amazonaws.com, and sign up for a new account using the new email addres
- When you are logged in, choose 'account' from the main menu, then 'security credentials'
- In the passwords file, record the email you used, and the 'access key ID' and 'secret access key'.
- Log in to your main AWS account using Cyberduck.
- Create a new bucket, called, for instance myproject.example.com
- Right-click the new bucket, click Info and click the Permissions tab
- Click the cog icon, then Amazon Customer Email address.
- Type aws-myproject@example.com. In the right column, choose WRITE
- Repeat the last two steps, but choose READ in the right column. (this step is optional)
- Your user now has read and write access to the myproject.example.com bucket.
Note that if you try to use Cyberduck to view the S3 account for the aws-myproject@example.com it will fail. This is because Cyberduck uses s3 features that assume that the account is signed up for S3 services (which requires a credit card). For the same reason using s3cmd (command-line tools for S3 acccess) to list all buckets will also fail. However, using s3cmd to view the contents of the specific bucket we have granted access to will succeed (for example s3cmd ls s3://myproject.example.com will work)
This tutorial assumes unfuddle, but will work for any third-party cloud service that wants to read or write to S3 buckets.
Thanks to Tom & Richard of Calvium for the idea, and for their help setting this up.
EDIT: 16-02-2011. This currently doesn't work properly on unfuddle due to their system failing in the same way that cyberduck does. Am in contact with them to sort it out

Hats off to your presence of mind..I really enjoyed reading your blog. I really appreciate your information which you shared with us.
ReplyDeleteAws Online Training
Positive site, where did u come up with the information on this posting? I'm pleased I discovered it though, ill be checking back soon to find out what additional posts you include.
ReplyDeletebinding mechine
I have read this post. collection of post is a nice one. Get touch with AWS Online Training Hyderabad Get more knowledge
ReplyDeleteAmazon has a simple web services interface that you can use to store and retrieve any amount of data, at any time, from anywhere on the web. Amazon Web Services (AWS) is a secure cloud services platform, offering compute power, database storage, content delivery and other functionality to help businesses scale and grow.For more information visit.
ReplyDeleteaws online training | aws training in hyderabad | aws online training in hyderabad